This article appears in the Fall-Winter 2019 digital issue of DOCUMENT Strategy. Subscribe.

Allison Lloyd serves as the Editor of DOCUMENT Strategy Media. She delivers thought leadership on strategic and plan-based solutions for managing the entire document, communication, and information process. Follow her on Twitter @AllisonYLloyd.

Image by: HAKINMHAN, ©2019 Getty Images
2019 was a year in which we saw robotic process automation, artificial intelligence (AI), low-code architectures, and conversational interfaces firmly take root within the enterprise. Leaders moved from grappling with these concepts to building out their business cases and pilot projects. However, along the way, we also discovered inherent challenges associated with process silos, digital ethics, security, and new skill sets required to set our transformative strategies in motion.
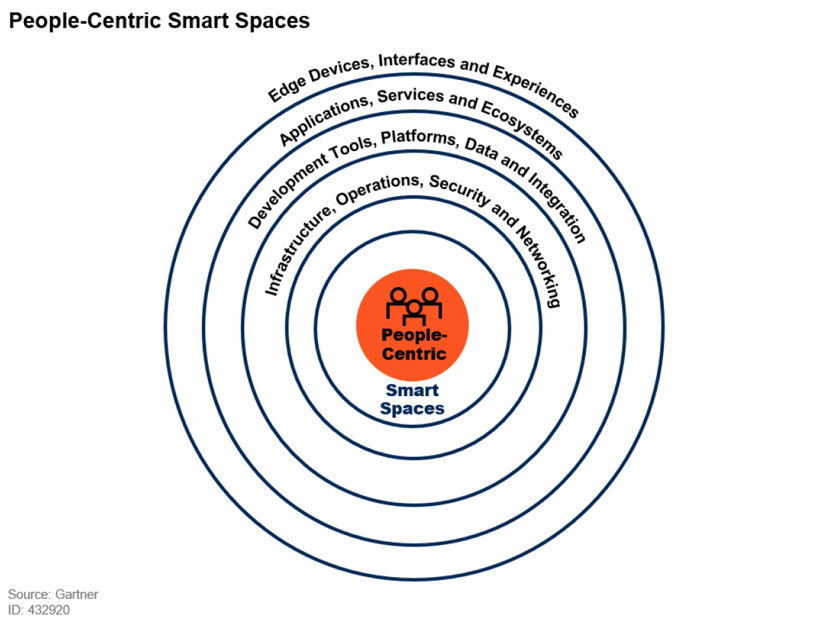
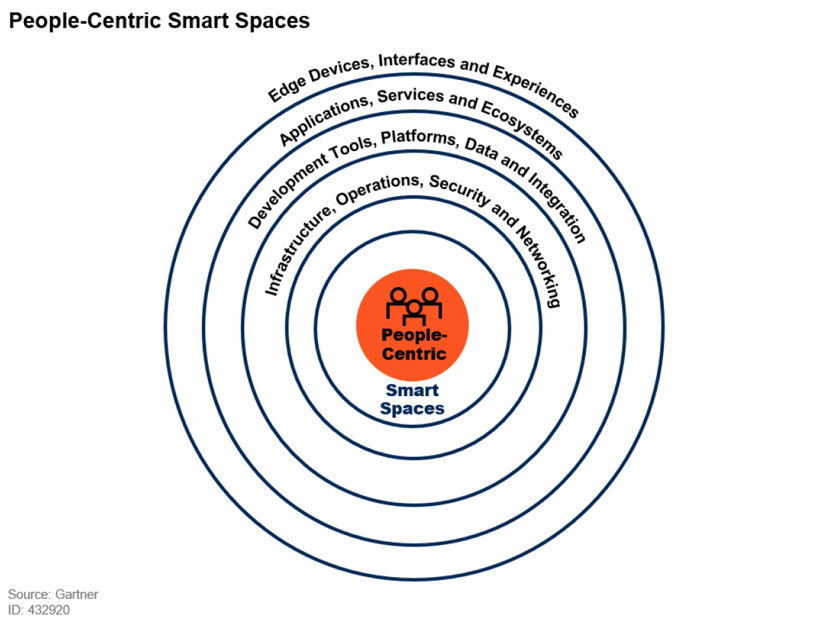
According to Gartner, those organizations who use AI for decision-making will need to account for shadow AI, which will pose the biggest risk to their ethical decisions. In Orlando at their annual IT Symposium/Xpo, Gartner Vice President and Fellow David Cearley emphasized that “putting people at the center of your technology strategy highlights one of the most important aspects of technology. Arguably, all actions of the organization can be attributed to how it impacts individuals and groups either directly or indirectly.”
As we look five years down the road at this disruptive technology landscape, enterprise leaders will need to understand the nuanced connections between people, processes, services, and things. Before we can build an innovative technology stack, we must first understand the business and human context for how these capabilities will help us to meet our desired outcomes. In their annual list of top strategic technology trends for 2020, Gartner calls this particular link “people-centric smart spaces,” a structure in which to evaluate the potential impact of the following strategic trends.
1. Hyperautomation
While robotic process automation (RPA) might have opened the door to hyperautomation, this trend involves multiple machine learning, packaged software, and automation tools (including RPA and intelligent business process management suites) to deliver work that once required human actions or execution. Hyperautomation not only refers to this expansive array of tools but also all the steps within the automation process as well. The power and breadth of hyperautomation opportunities have been enhanced by AI capabilities, like machine learning and natural language processing (NLP), leading to vendors fiercely competing to outmaneuver each other on this front.
2. Multiexperience
In today’s digital-first world, consumers are demanding an effortless experience as they jump from device to device or on multiple devices simultaneously. The multiexperience is defined by how users perceive and interact with the digital world. Conversational platforms (with multisensory capabilities, like sight, taste, smell, and touch) are changing the way we interact with the digital world, while virtual reality, augmented reality, and mixed reality are changing the way we perceive it. However, supporting the multiexperience requires a flexible back end to support the different capabilities and workflows across every app.
3. Democratization
In this new age of technology, reskilling and reassigning knowledge workers will be a critical enabler for enterprise transformation, and we will need solutions to facilitate ease-of-use and speed to market for non-technical business users. This is leading to the rise of citizen development and low-code/no-code models, which provides the required technical and domain expertise without extensive training. According to Gartner, low-code application development will be responsible for more than 65% of application development by 2024. Furthermore, the use of virtual assistants or expert systems, based on AI and decision models, will also help to extend the knowledge or expertise of the current workforce.
4. Human Augmentation
Throughout history, humans have used tools to enhance their capabilities and performance. Today, technologies like the Internet of things (IoT), AI, smart speakers, and VR are offering opportunities for human augmentation in totally new ways. This augmentation allows us to achieve digital transformation through human transformation. As a result, enterprises of all types and sizes are considering human augmentation to achieve various business outcomes. Before organizations embark on new use cases for human augmentation, they must examine the security, privacy, compliance, health, and ethical impacts along the way.
5. Transparency and Traceability
The evolution of AI and machine learning offer great rewards and even greater risk. As organizations continue to embed more intelligent decision models within their applications and expose these capabilities to a larger swath of knowledge workers, the more they will have to face the digital ethics and privacy concerns that come with such innovations. In fact, 30% of government and large enterprise contracts for digital products and services using AI will require the use of explainable and ethical AI, according to Gartner. Ultimately, trust is earned from demonstrable actions over time. This will require organizations to shift their privacy policies from being compliance-driven to ethics-driven.
6. The Empowered Edge
Edge computing is the concept of processing and collecting content closer to the direct source, repository, or consumer of information. It has historically solved issues such as high bandwidth costs and unacceptable latency. While most use cases for edge computing have been focused on IoT systems or devices, its adoption will accelerate across all industries as the edge is enabled with more sophisticated compute resources and data storage. By 2022, 75% of enterprise-generated data will be created and processed outside the traditional, centralized data center or cloud, according to Gartner. This will push modern use cases to include more and more edge requirements to support these new distributed data architectures.
7. Distributed Cloud
The evolution of the distributed cloud shakes up the centralized model of most public cloud services—and marks a new era in cloud computing. The distributed cloud allows the distribution of public cloud services to different locations outside of the cloud provider’s data centers but still maintains control over the operation, governance, maintenance, and updates of their cloud services. While the distributed cloud is still in the early stages of development, some offerings include Microsoft Azure Stack, Oracle Cloud at Customer, Google Anthos, IBM Red Hat, and Amazon Web Services Outposts.
8. Autonomous Things
This term may bring to mind robots, drones, autonomous vehicles, and appliances. While autonomous things can range from semi-autonomous to fully autonomous, Gartner defines these objects as “things that can operate unsupervised within a defined context or to complete a task.” No matter the level of automation, autonomous things can’t hope to match the human brain. Organizations can leverage specific business environments and customer journey maps to find opportunities for automating manual tasks with these intelligent devices.
9. Practical Blockchain
According to the 2019 Gartner CIO Survey, 60% of chief information officers expect to deploy some application of blockchain technology in the next three years. In a time where transparency and traceability are paramount, blockchain provides a mechanism of trust, eliminating the need for a central authority in the transaction. While it remains a key building block to digital transformation, enterprises struggle to overcome the challenges of scalability and interoperability. Current use cases for blockchain include asset tracking, claims processing, identity management, internal recordkeeping, tracking loyalty points and providing rewards, payments/settlements, recording the movement of assets, shared recordkeeping, smart cities, trade finance, and trading.
10. AI Security
The prevalence of IoT, cloud computing, microservices, and highly connected systems in the enterprise creates new vulnerabilities for malicious attacks and introduces unanticipated security risks. Security and risk professionals will need to protect their AI-powered systems, leverage AI to enhance security defense, and anticipate nefarious use of AI by attackers. A new class of machine learning-based security tools can be a powerful weapon for security monitoring, malware detection, or network anomaly detection.







