Image by: Ingram Publishing, ©2016 Getty Images
Documents, specifically records, do not spring into being for no purpose; they are created in support of business activities. Information governance (IG) is all about keeping track—who, what, when, where, how—of business functions and the activities that support them. While managing records will always be important, it is also likely that the history of how that document flowed through an organization—its provenance—could be just as important.
There are a thousand benefits from using business process management (BPM)/workflow to facilitate IG. Sarbanes-Oxley (SOX) triggered a slew of specialized workflow solutions for the purpose of managing financial data and approvals necessary for SOX reporting, but broader business process automation using BPM will bring significant IG benefits to any organization.
When documents/records are created or added within a BPM instance, they are, by default, properly categorized without any additional human interaction. Document categories (or types) are linked to the retention schedule, allowing for automatic life cycle control, especially when using a document management solution. Plus, BPM keeps an audit trail of every action taken, every data element added or changed, approvals, all routings, etc., with date and time stamps all along the way.
Governance rules are effectively mandated and audited for compliance with no additional effort when using BPM. Compare this approach to management-by-email: How often, in your own environment, does an overlooked email affect timelines of work? It’s just too easy for process flows to be broken with an ad‑hoc approach like email.
Too often, though, deploying BPM is considered complex, expensive, and time-consuming. It can be with high-volume, transactional processes like claims processing, but it doesn’t need to be nor should it be for typical compliance processes. Value will be realized faster if workflow can be deployed quickly. My rule is, "Workflow deployment success is inversely proportional to deployment time." In other words, deploy simply and quickly but have a program of continuous process improvement to enhance the process over time.
Even a simple and quick deployment yield significant benefits. Take the simplest of workflows using a personally identifiable information (PII) breach as an example.
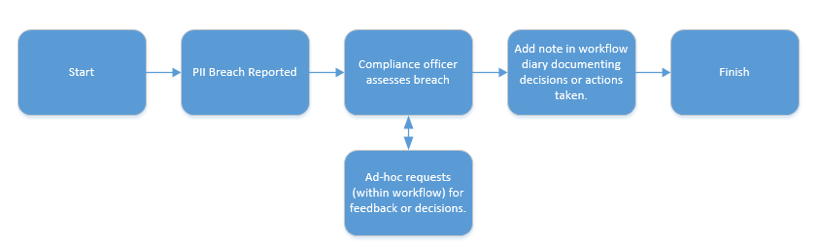
©2016 IMERGE Consulting, Inc.
Even though there are no business rules, data lookups, or sophisticated routings, the process flow will gather in the audit trail:
- Incident report date and time
- Reporting individual
- Date and time compliance officer received the breach notice
- All individuals involved in review or approval (ad-hoc tasks)
- Breach resolution notes (workflow diary)
- Total time from breach incident, open to closed
If you aren’t using BPM to facilitate IG compliance, take the initiative to launch an automation program today; you’ll be glad you did. If you want more discussion on how BPM can be used for IG compliance, let me know, and I’ll expand on this discussion in a later post.
Jim Just is a Partner with IMERGE Consulting, Inc., with over 20 years of experience in business process redesign, document management technologies, business process management, and records and information management. Contact him at james.just@imergeconsult.com or follow him on Twitter @jamesjust10.